How to prepare your organization for the new NIS 2 Directive?
If (cyber)security was not the first topic on the agenda of the Board of your organization since 2016 (NIS 1), then it will be now. The NIS 2 (Network & Information Security 2) directive of the EU not only expands the scope of the legislation, but also the industries who need to take adequate measures to protect the European economy and society.
Where GDPR focuses on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, NIS targets operators of essential services and digital service providers across 18 sectors such as energy, finance, healthcare, and transportation. These sectors are required to invest in cybersecurity measurements, incident reporting, and supply chain security.
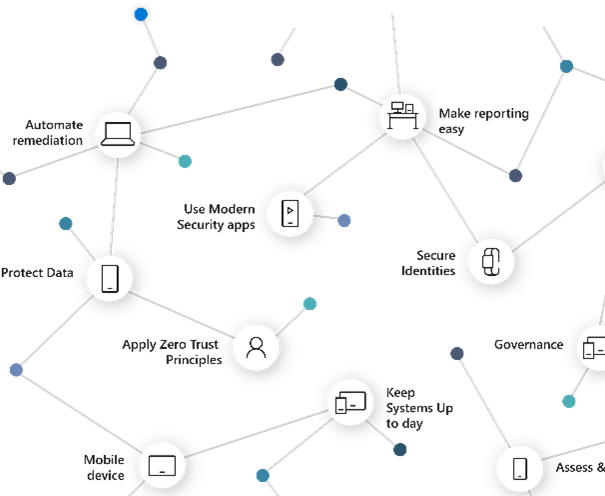
For the IT staff, article 21.1 of this regulation matters most. It states that your IT strategy will be based on an all-hazards approach that aims to protect network and information systems and the physical environment of those systems from incidents. For this reason, all specialists recommend organizations to build a governance framework with remediation mechanisms to comply with this objective and with their own ambitions to protect and secure.
Prepare your organization for NIS 2
Focus Area
Practices
Appdate
Organization of Information Security
- Security Ownership
- Security Roles and Responsibilities.
- Risk Management Program
Asset Management
- Asset Inventory
- Asset Handling
- Security Training
Physical and Environmental Security
- Physical Access to Facilities
- Physical Access to Components
- Protection from Disruptions
- Component Disposal
Communications and Operations Management
- Operational Policy
- Data Recovery Procedures
- Malicious Software
- Data Beyond Boundaries
- Event Logging
Access Control
- Access Policy
- Access Authorization Least
- Privilege Integrity and Confidentiality
- Authentication
Information Security Incident Management
- Incident Response Process
- Service Monitoring
Business Continuity Management
- Emergency and contingency plans
- Redundant storage and its procedures for recovering data

The GDPR requires all organizations, whether within the EU or not, to protect the personal data of EU citizens.

The NIS 2 directive requires sectors providing services of high criticality or critical services related to EU infrastructure, to implement appropriate measures to minimize potential incidents, encompassing all aspects of security.
